OpenSOC: Building an Open Source SOC Lab That Does Not Suck
Contents

about this project
OpenSOC is my SOC lab. This series is me documenting how I built it and why I made certain decisions, mostly so I don’t forget when something breaks six months from now.
I’ve been doing SOC/NOC work, messing with SIEMs, Meraki firewall and MDM, endpoint monitoring and pentesting for about a year now. And the one thing that pisses me off about security work is that there’s no clean paper trail. With software you have commits, PRs, test results, you can see progress. Security work just explodes into a hundred different places. alerts here, firewall rules there, some dashboard you screenshotted at idk when everything was burning down, investigation notes in a random text file, RCA nobody reads. Its a fucking mess and that knowledge just evaporates.
So I’m writing this down. for me, and for you when you inevitably break the same shit I did.
The idea is a lab that’s actually small enough to understand, not some enterprise fantasy setup you copy paste without knowing what half of it does. modular too, so it grows without having to burn everything down and start over.
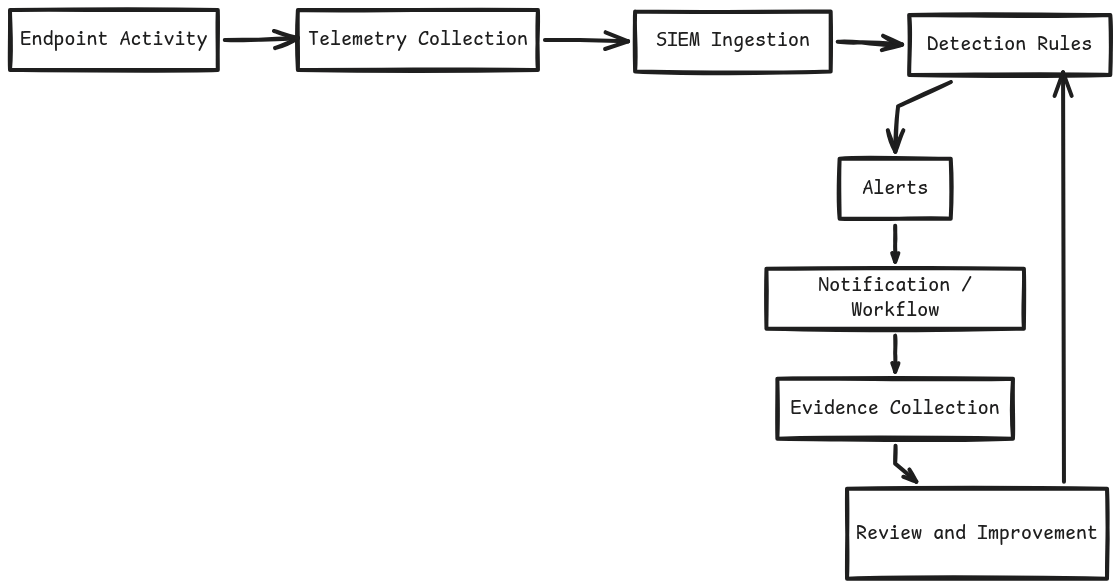
The loop looks like this:
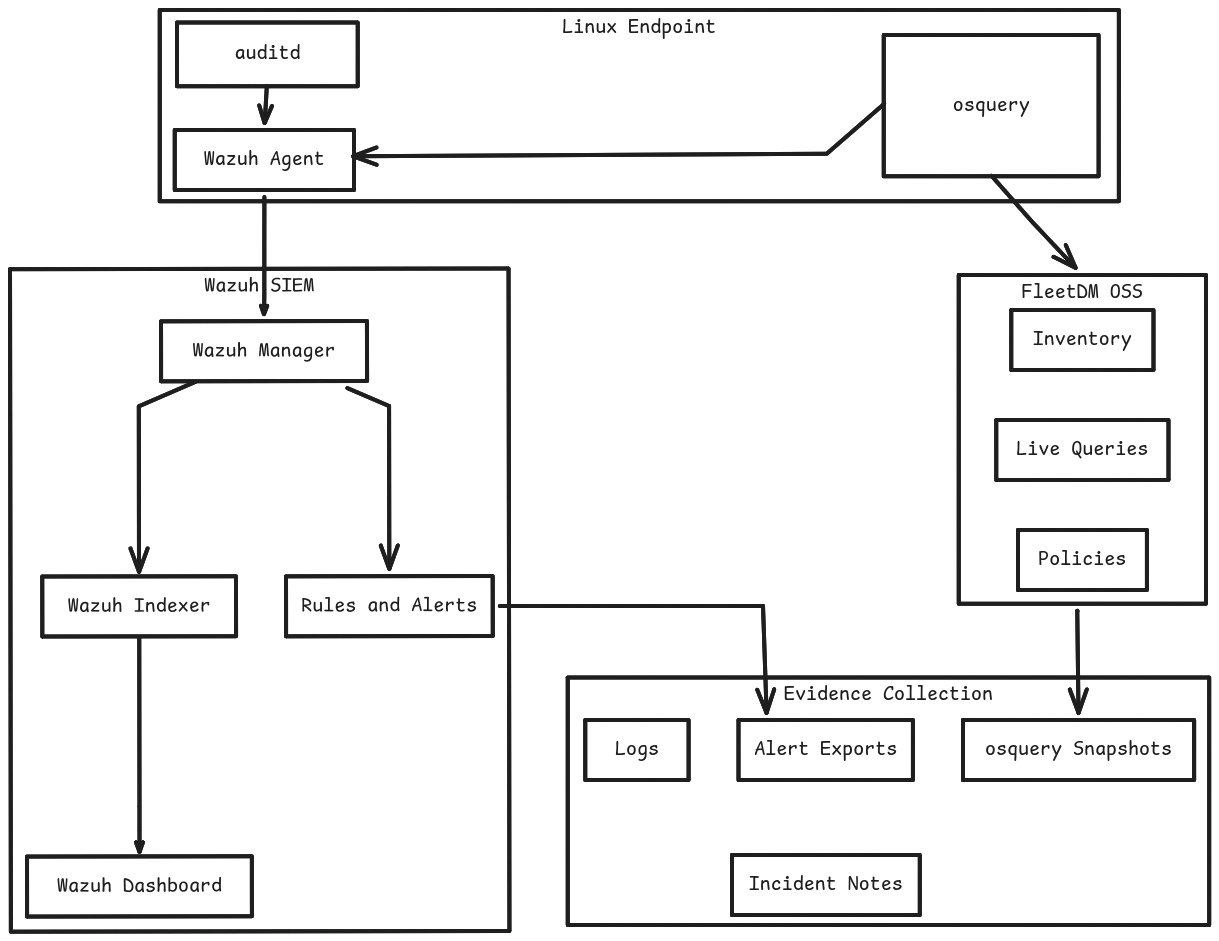
Starting with wazuh as the SIEM. linux endpoint monitoring with wazuh agent, auditd and osquery. FleetDM OSS for fleet management. basic detections, alerting, evidence collection. nothing fancy, just stuff that actually works.
Current shape of the lab:
Eventually this grows into suricata, zeek, SOAR, windows and macOS agents, splunk, the whole enterprise thing. but i’m not writing about things I haven’t built yet. that’s how you end up with documentation that’s useless because half of it is theoretical bullshit.
This post is just the intro and the design. part 2 is where the actual setup begins.